By: Ethan Howland
• Published April 18, 2025
The power grid performed well during extremely cold weather in January, a sign that steps taken since previous winter storms are paying off with improved electric reliability, according to a report released Thursday by the Federal Energy Regulatory Commission and the North American Electric Reliability Corp.
About 71 GW of generation was unexpectedly offline during winter storms in January that covered most of the United States, according to the report. About 91 GW was unexpectedly offline during Winter Storm Elliot, which mainly affected the Eastern Interconnection in December 2022.
There were no power outages in January, while grid operators instituted rolling blackouts totaling 5,400 MW during Elliott and 23,418 MW during Winter Storm Uri, which mainly affected Texas and the Southcentral U.S. in February 2021. The Texas Department of State Health Services estimates that 246 people died as a result of Uri, mainly from hypothermia as well as the use of alternate heating sources while their power was out.
Several factors appear to have contributed to the improved performance during the most recent bout of extremely cold weather, including improved communication and coordination between the natural gas and electric industries, according to the report.
Among the positives during January’s bitter cold, the PJM Interconnection exported 7,650 MW during a peak demand period, according to the report. Several electric entities declared “conservative operations” earlier than in past events to delay or cancel planned transmission outages to reduce grid congestion and enhance transfer capability, FERC and NERC staff said in the report.
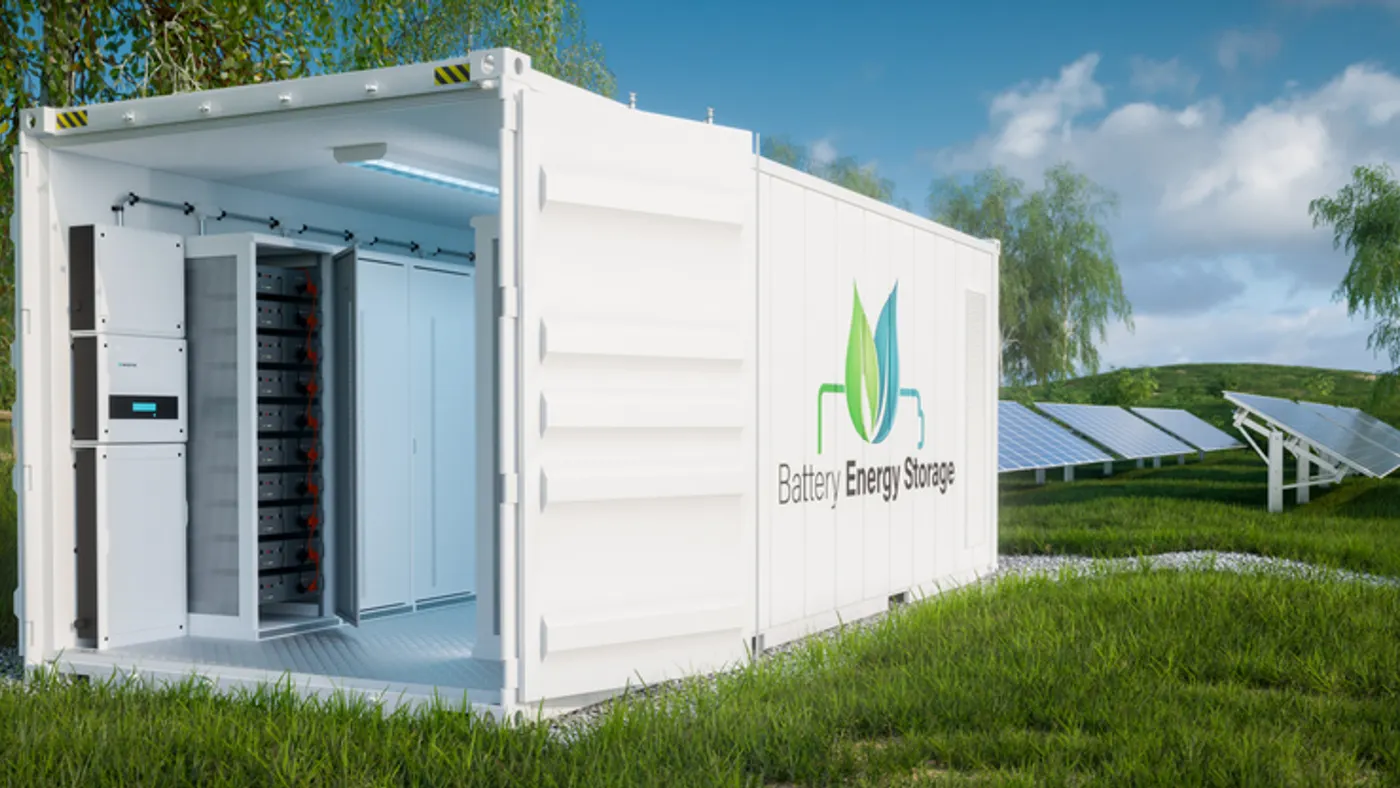
Also, several entities surveyed by staff said battery storage helped their performance during the January arctic events, according to the report. “ERCOT stated that the rapid deployment of battery storage resulted in batteries providing 3,800 MW at peak times, alleviating stress on the grid during critical demand hours,” staff said.
Grid operators’ demand forecasts were more accurate than in the past and there was increased data sharing between generators and gas pipeline operators, which helped ensure power plants had fuel to burn, according to the report.
In comments on the report, FERC Chairman Mark Christie highlighted the role the Mountain Valley gas pipeline played in keeping the gas system operating and supporting electric reliability. Also, PJM’s ability to export power may shrink as its power supply margins fall, according to Christie. “You can't export something you don't have, and as PJM loses its surplus generating resources, there won't be anything to export,” he said. “That's a huge problem.”
Even with the grid’s improved performance in January, the United States needs more energy infrastructure, according to Commissioner Willie Phillips. “The more energy infrastructure we get on the system, the easier it is for us to provide power to the American people, our homes, our business, to provide it in a way that they can actually afford it,” he said.
Here are four other takeaways from the meeting.
NERC eyes data center reliability impacts. NERC is exploring how data centers and cryptocurrency operations could affect grid reliability and whether standards are needed for those facilities, according to Mark Lauby, senior vice president and chief engineer at the grid watchdog organization.
As an example of the potential problem, about 1,800 MW of data center load went offline suddenly in northern Virginia in February and about 1,400 MW went offline in July, Lauby said at the FERC meeting. From November 2023 through January, there were 25 crypto mining load loss events in ERCOT, ranging from 100 MW to 400 MW. The sudden loss of load can affect the grid’s voltage and frequency, and potentially lead to wider power outages, Lauby said.
A NERC large load task force aims to develop risk mitigation guidelines by early next year, according to Lauby’s presentation. There are a “host of solutions” for dealing with large load risks, Lauby said.
Christie defends PJM. Christie, a self-described critic of PJM’s capacity market, defended the organization and its staff during the open meeting. “A lot of this criticism I have seen in the media, directed at PJM and its management, and blaming them for everything that’s wrong with the PJM capacity market, I think is in many ways misplaced,” Christie said. PJM’s staff “work very hard, and work in good faith.”
In part, problems related to the capacity market are driven by choices some states made about 20 years ago when they decided to rely solely on PJM’s capacity market for their power needs, Christie said during a media briefing.
Christie declined to respond directly to New Jersey Gov. Phil Murphy’s request that FERC investigate a capacity auction held in July that saw capacity prices jump to about $270/MW-day for most of the grid operator’s footprint, up from about $28/MW-day in the previous auction. The increase is leading to significant rate hikes in some states starting June 1 when the next capacity delivery year begins.
FERC has so many cases involving PJM that the agency is constantly investigating the grid operator in a general sense, Christie said. FERC is holding a two-day technical conference in early June to explore capacity markets and other approaches to ensuring there are adequate power supplies.
Christie: PJM-Transource stance “utterly outrageous.” Christie slammed arguments made in court by Transource — an American Electric Power and Evergy joint venture — and PJM that transmission projects included in the grid operator’s regional transmission expansion plans are exempt from state certificate of public need reviews.
The stance is an “utterly outrageous position” and runs counter to commitments AEP and Dominion Energy utilities made in 2004 when they sought to join PJM, Christie said during the media briefing. If Transource wins its case, states may reconsider allowing utilities to be members of regional transmission organizations, Christie said in a concurrence to an order issued Thursday. “As the debate continues over whether to give transmission developers/owners a perpetual [return on equity] adder for joining an RTO, the history recited herein is extremely relevant,” Christie said.
FERC staffing expected to fall. FERC is in a hiring freeze and its headcount is expected to fall by 9% by the end of its fiscal year, Christie said during the media briefing. FERC had a staff of about 1,500 people as of December. The agency expects 55 staff members will accept a deferred retirement offered by the Trump administration, Christie said.
“We want to keep the key people,” Christie said, pointing to FERC staff involved in natural gas permitting. “We don't want to lose people who are essential to getting those permits out.”
Phillips offered support for FERC staff amid Trump’s efforts to slash the federal workforce. “It's not exactly an easy time to be a federal employee right now, and I think it's worth being said that the work you do is outstanding,” Phillips said. “We're busy … and we're doing a lot of great work for the American people.”
Article top image credit: AerialPerspective Works via Getty Images