Dive Brief:
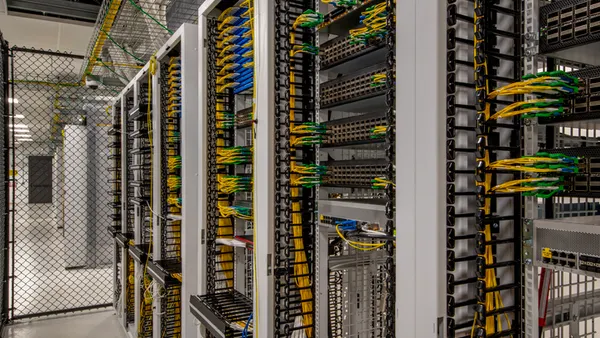
- Cybersecurity firm Dragos has secured a $10 million investment from the utility-backed firm Energy Impact Partners and two other companies to assist in growing its global workforce to meet demand for the company's services.
- Cybersecurity is a growing concern in the electric utility industry. Over the summer, Dragos issued a report concluding malware used in a 2015 cyberattack against the Ukrainian power grid could be modified to disrupt U.S. utilities.
- The new investment was co-led by EIP and Allegis Capital, with additional support from DataTribe, a cybersecurity startup that initially funded Dragos. EIP's backers include Southern Company, National Grid, Xcel Energy, Ameren, Great Plains Energy and others.
Dive Insight:
Industry polling shows cybersecurity ranks at or near the top of critical concerns for utility executives. Now a prominent IOU-backed investment firm is getting in on the game.
The $10 million investment from a trio of companies is EIP's first funding for a cybersecurity firm .
"One of the critical challenges in [industrial control system] security is access to sufficient human capital," EIP Vice President Sameer Reddy said in a statement.
The funding will be used to increase the company's workforce. Rising demand for its cybersecurity services is being generated through key partnerships with Deloitte, according to a press release.
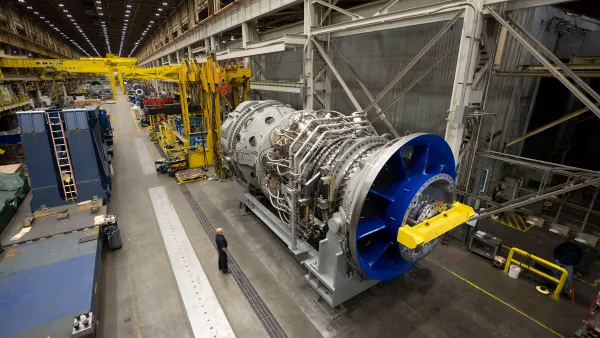
The company says it "exists to safeguard civilization," specializing in protections for power plans, manufacturing, water infrastructure, petrochemicals and oil.
This summer, Dragos issued a report analyzing malware that was used in a 2015 cyberattack that caused a widespread blackout in Ukraine. The firm determined the malware could be modified by its Russian developers to target the United States.
According to the report, the program — dubbed "CrashOverride" — was just the second industrial control system-tailored malware to target physical industrial processes.
The North American Electric Reliability Corp. issued a Level 1 alert in the wake of Dragos' revelations. According to NERC's alert, the malware can "cause loss of visibility, loss of control, manipulation of control, interruption of communications, and deletion of local and networked critical configuration files."