Dive Brief:
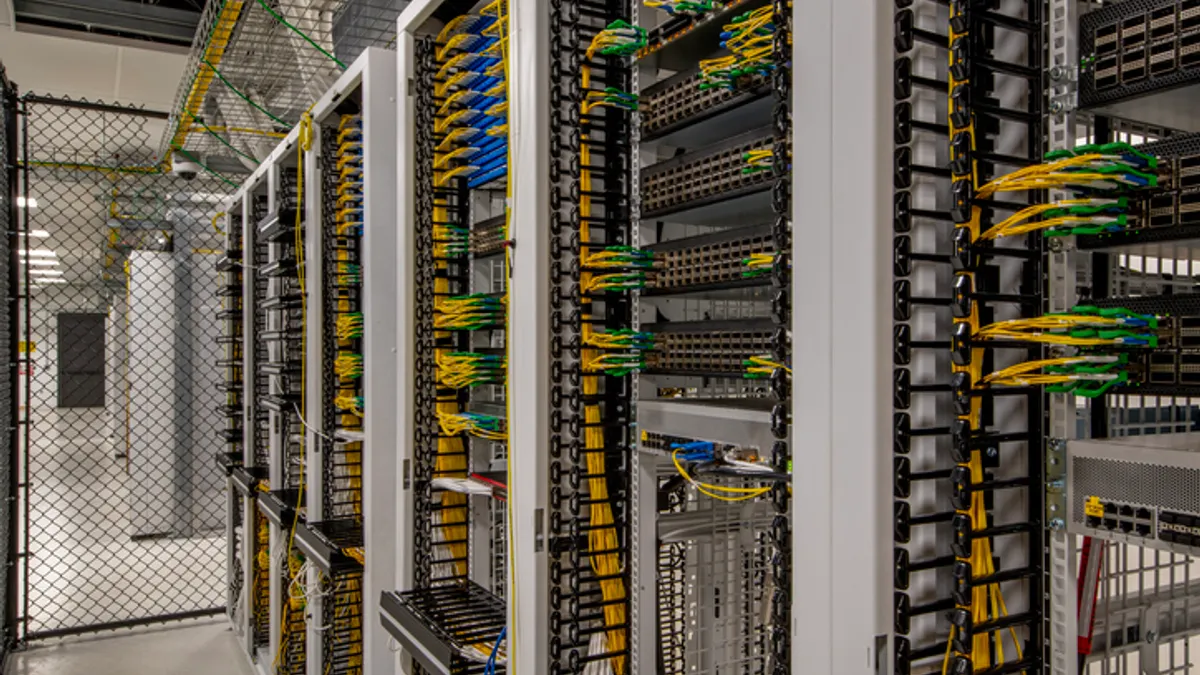
- The Federal Energy Regulatory Commission on Wednesday published a notice of inquiry (NOI) on cybersecurity issues, including how "a coordinated cyberattack on geographically distributed targets" could disrupt the grid and potential measures to counter the threat.
- The commission is soliciting comment on whether Critical Infrastructure Protection (CIP) Reliability Standards adequately address cybersecurity risks pertaining to data security, the detection of anomalies and events, and the mitigation of cybersecurity events.
- The NOI asks for input on potential solutions, including potential modifications to the current megawatt thresholds governing CIP standard applicability to bulk electric system (BES) facilities.
Dive Insight:
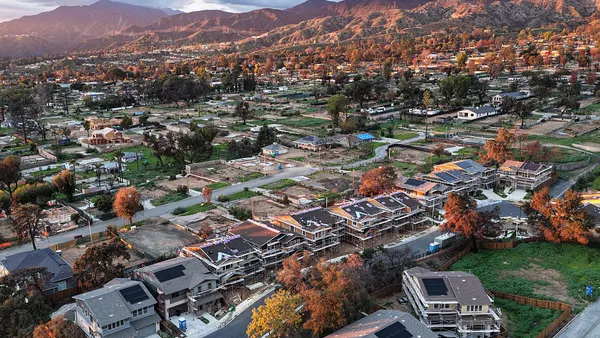
As more distributed resources and industrial control systems (ICS) are connected to the nation's electric grid, experts say it creates a potential vulnerability that is not clearly understood and could be exploited to cause power instability and blackouts.
FERC's inquiry stems from a September 2019 report from the U.S. Government Accountability Office that concluded the U.S. electric grid "is becoming more vulnerable to cyberattacks," with ICS and the rise of distributed resources playing major roles in the growing risk.
While the U.S. power system has avoided a major disruption caused by hackers, there have been attacks and there is proof the threat to energy systems is real. In 2015, Ukraine suffered a major blackout caused by an ICS attack. More recently, a ransomware attack shut down a natural gas compressor station in the United States for two days.
"It's no surprise that cyber security threats have crippled critical infrastructure over the past decade," Mike Almeyda, account manager at security services firm Force 5, told Utility Dive. "Fortunately, there has been a good foundation of information sharing as each event has occurred."
Now FERC wants to take a closer look at the threat and is asking industry to share information about potential vulnerabilities and whether the existing standards sufficiently mitigate them. The commission is seeking comment on whether the current CIP standards adequately address aspects of the National Institute of Standards and Technology's (NIST) Cyber Security Framework, and how to address "potential reliability gaps" between the two.
FERC is requesting comment on "the risk of a coordinated cyberattack on the bulk electric system and potential commission action to address such risk." According to the NOI, "the commission has questioned whether greater defense in depth is warranted to better protect the bulk electric system from a coordinated attack on multiple BES Cyber Assets."
The NOI seeks comment on possible enhancements to the current CIP standards, but would not expand the definition of the bulk electric system nor would it expand the standards to cover non-BES facilities used in local distribution.
The inquiry does ask whether, as the BES evolves to include more smaller, geographically distributed generation resources, if there is a need to modify CIP standards that may be focused more on traditional large generating facilities. And it considers whether the integration of small, geographically distributed generation resources that are categorized as low impact cyber systems and, therefore, not required to comply with the full suite of CIP standards, pose a reliability risk, particularly from a coordinated cyberattack.
FERC's inquiry will consider:
- whether CIP standards adequately address data security for low, medium and high impact BES systems;
- if low impact BES cyber systems need to be be covered by certain NIST data security requirements;
- whether there are operating processes and procedures that can be used to counter and recover from "potential geographically distributed coordinated cyberattacks;"
- the effectiveness of industry information sharing at mitigating potential coordinated cyberattacks;
- and possible changes to the bulk electric system design that could affect the potential risks of those attacks.
The CIP standard for categorizing BES cyber systems is effective in the way it evaluates individual systems, said Almeyda. "But I think the true question should be whether distributed resource thresholds should be defined as an addition to the impact rating criteria," he said. "Perhaps that could help determine the true risks of coordinated attacks, as the NOI suggests."
Comments on the NOI are due within 60 days, and reply comments are due 30 days after that.