Two evolutions are taking place around the power sector today, which could make it more difficult to defend from a growing cyber threat.
Hackers are becoming increasingly sophisticated in their attempts to disrupt electric grids. Attacks are more targeted, including spear phishing efforts aimed at individuals, and are shifting from corporate networks to include industrial control systems.
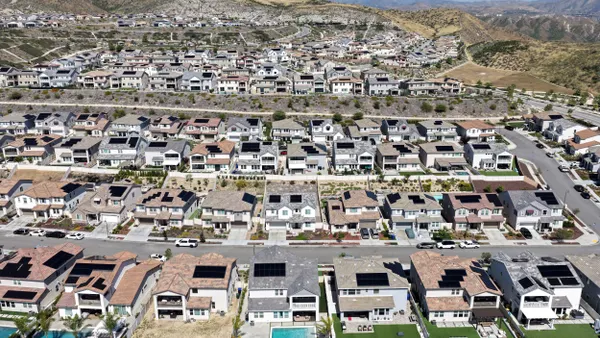
At the same time, the grid is becoming increasingly distributed and connected. Older power plants have been spared cyber attacks because they were not connected to the internet (which may not have existed when they were built). New resources are connected — though they are also being constructed with security in mind. And in this growing Internet of Things world, just about every device imaginable can create a potential vulnerability.
This creates something of a double-edged sword, say security experts. On the one hand, it distributes risk and the consequences of a successful breach. But it also creates a broader "attack surface" with more vulnerabilities and opportunities for attackers to gain access.
"In theory, a grid with more distributed resources can increase the potential attack surface for adversaries because the capacity of distributed generation, including renewables, has grown exponentially over the last decade."

Bill Lawrence,
Director, NERC's Electricity Information Sharing and Analysis Center
"Modern grid technologies expose existing security vulnerabilities in new ways, as well as introduce new benefits," Advanced Energy Economy Institute concluded in an assessment of cybersecurity challenges on a distributed grid, published earlier this year.
The report also found the energy industry is "learning important lessons from the high profile, and high impact, attacks that have affected a large number of users in the United States during the past two years." AEEI noted that several attacks have used internet-connected devices "such as baby monitors, webcams, and other smart home devices."
No major disruptions yet
Thus far, the utility sector in this country has dodged any major disruptions due to cyberattacks. There have been minor intrusions, malware infections and false alarms, but so far, hackers have not been able to turn off the lights. Increasingly, however, security experts concede a successful attack is likely to happen eventually.
"In theory, a grid with more distributed resources can increase the potential attack surface for adversaries because the capacity of distributed generation, including renewables, has grown exponentially over the last decade," Bill Lawrence, director of NERC's Electricity Information Sharing and Analysis Center, told Utility Dive in an email.
Some of the success in deflecting attacks so far, said Lawrence, is because many of the new distributed resources are including cybersecurity concerns and plans from the start of a project, and up-to-date security solutions are coming to market. Some of those security products, he said, have been developed through the Department of Energy's Cybersecurity for Energy Delivery Systems research and development program.
DOE's Office of Electricity developed the R&D program, aiming to help energy sector asset owners. The Office of Electricity's website neatly presents some of the difficulties presented by distributed resources.
While the electric grid is undoubtedly becoming more distributed, Lawrence said that so far there has not been an increased risk to the security and reliability of the bulk system. There are two reasons for that, and the first one could be changing.
"First, distributed resources still provide a small percentage of the overall electricity consumed in North America each year," Lawrence said. "Second, the intermittency of distributed resources already requires grid operators to call on baseload generation to maintain the reliability of the bulk power system by offsetting the frequent reductions in output from solar, wind and other distributed generation."
Lawrence said NERC expects those baseload resources to also be available "in the unlikely scenario that one or more distributed resources became unavailable due to a cyber or physical attack on those facilities."
A turning point in Ukraine
It has happened before: In December 2015, cyberattacks caused widespread blackouts in Ukraine, and since then, the incident has heightened fears and awareness in the United States. Two years later, Sen. John McCain, R-Ariz., confirmed Russia has the capability to shut down American power plants through hacking efforts. And cybersecurity firm Dragos determined the malware used in the Ukraine attack could be modified by its Russian developers to target the United States.
The cyberattack in Ukraine may represent a turning point in the security battle.
The malware used in the attack, named "CrashOverride," was only the second industrial control system-tailored malware to target physical industrial processes, according to Dragos. The first was Stuxnet, designed by the United States and Israel to disrupt Iran’s nuclear program and identified less than a decade ago.
Since Ukraine, however, there have been other reports of cyberattacks on industrial control system equipment. Hackers last year were able to penetrate the safety systems of a petrochemical plant in Saudi Arabia, in part by taking advantage of an older device made by Schneider.
-
2010
Stuxnet
First virus to target industrial control systems; thought to be developed by the U.S. and Israel to disrupt Iran's nuclear program.
-
November 2013
GridEx II
North American Electric Reliability Corp. hosted their second simulated grid attack, aimed at helping utilities hone their response plans. 234 organizations and 2,000 individuals participated.
-
November 2014
Sony Pictures
Hackers steal unreleased films and confidential emails from the film studio. Thought to be retaliation for "The Interview," a satire about the assassination of the North Korean leader.
-
December 2015
Ukraine
First successful cyberattack on a power grid, targeting substations; up to a quarter million people were without power for hours. Russian hackers thought to be behind the attack.
-
December 2016
Vermont false alarm
Retracted reporting by the Washington Post leads to false widespread reports of Russians hacking Burlington Electric, in Vermont.
-
May 2017
WannaCry
Global four-day ransomware attack hits upwards of 200,000 computers in about 150 countries; damages estimated into the billions.
-
August 2017
Saudi Arabia
Another hack on an industrial control system, involving older Schneider-made equipment at a petrochemical plant.
-
November 2017
GridEx IV
NERC's biennial event roughly doubled in four years; more than 450 participating organizations and 6,500 individuals.
-
February 2018
Entergy malware
Midcontinent ISO raised its system status level to "orange" after a malware discovery which only impacted Entergy's corporate network and some employee devices.
-
April 2018
Gas pipeline comms breach
Hackers shut down a communications network used by Energy Transfer Partner's pipeline system and others in the oil and gas sector. Duke Energy of Ohio shut down portions of its system as a precaution, resulting in billing issues.
10 years of a growing cyberthreat
Eddie Habibi, founder and CEO of cybersecurity firm PAS Global, says there is a risk of underestimating the threat, which is dangerous and widespread.
"We have an entire industry — not just industry, but the entire industrial sector — that we believe is at risk," he said. "These systems were never designed with security in mind. They are vulnerable, and control the critical infrastructure of every nation."
Up to $1 trillion in damages
Lloyd's of London issued a report three years ago estimating the potential impacts of a widespread attack on the U.S. power grid. The firm concluded the total economic loss could range from $243 billion up to $1 trillion in the most damaging scenarios.
Given such potential impacts, cybersecurity is of paramount importance in the utility sector, and efforts to harden defenses are ramping up quickly.
Several surveys of executives in the energy space, including Utility Dive's own, have shown many think a successful attack is likely in the next few years. Last year, a report from consulting firm Accenture found 76% of utility executives expect it to happen within the next five years.
The threat has caught the attention of the federal government. This month, DOE published a five-year plan to diminish the risk of energy disruptions due to cyberattacks, focused on strengthening preparedness, coordinating responses, and developing the next generation of resilient energy systems. And in February, the Trump administration announced it would develop The Office of Cybersecurity, Energy Security, and Emergency Response, which will focus on energy infrastructure security and be funded through $96 million in the White House's Fiscal 2019 budget request.
"You can never avoid cyber incidents. Cyber is inevitable. It will happen to some companies. So as one plans their cyber strategy, they also have to plan a response."

Eddie Habibi
Founder and CEO, PAS Global
Regarding other federal activities related to grid cybersecurity, the Federal Energy Regulatory Commission in April approved a revised Critical Infrastructure Protection reliability standard directing NERC to make changes to standards to "further mitigate the risk of malicious code" from devices like laptops and thumbdrives.
Looking at the distributed grid, AEEI's report on cyber threats recommended creation of "guidelines for implementing reliable and secure DER systems," along with "coordination and unification of DER cybersecurity efforts." Ultimately, the report finds the distributed grid to be a net-positive for resilience and security.
"The adoption of [distributed energy resource management systems] by utilities and other grid operators may create an additional opportunity to further harden the cybersecurity of intelligent grids," the report concluded.
"The outlook on grid edge security should be positive."
Despite all the focus on defense, Habibi says the most important thing for utilities may be to have a response plan.
"You can never avoid cyber incidents," he said. "Cyber is inevitable. It will happen to some companies. So as one plans their cyber strategy, they also have to plan a response."